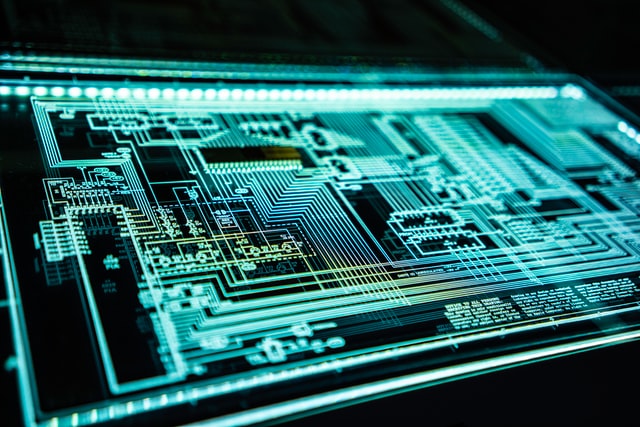
You might think that typing on your laptop in a coffee shop or during a Zoom call is safe and private. However, researchers have found that it's possible for someone to "listen in" on your keyboard and figure out what you're typing. This may sound like something out of a spy movie, but it's a very real concern.